(302) 262 8484
Exactly What to Do When Your Business Experiences a Ransomware Attack
Seeing a red screen demanding cryptocurrency is a nightmare for any founder or IT director. Panic sets in fast. But what you do in the first few minutes after your business experiences a ransomware attack will dictate whether you lose a few hours of work or your entire company.
If you are reading this while under active attack, take a deep breath. You need to act fast, but you need to act smart.
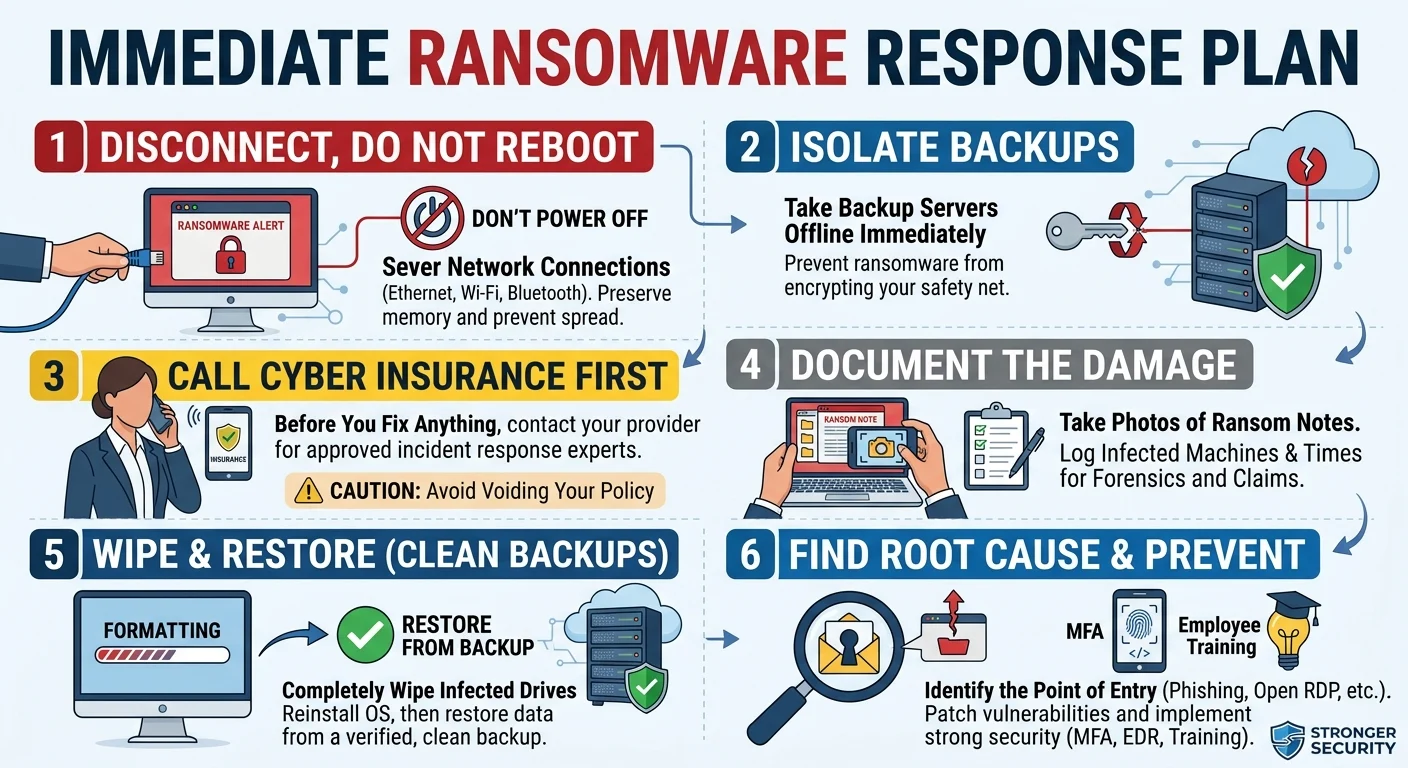
Here is a quick checklist of your immediate response plan to stop the damage:
- Disconnect infected devices from the network immediately.
- Do not turn off or reboot the compromised computers.
- Take backup servers offline to prevent the infection from spreading to your safety net.
- Call your cyber insurance provider before you try to fix anything yourself.
Let us break down the exact steps to contain the threat and get your operations back online without destroying vital evidence.
Step 1: Disconnect, Do Not Reboot
Your first instinct might be to pull the power cord on the infected computer. Do not do that. Powering down a machine can destroy volatile memory that forensic experts need to figure out exactly how the attackers got in.
Worse, some ransomware is designed to permanently corrupt your hard drive if it detects a sudden reboot.
Instead, physically disconnect the ethernet cable. Turn off the Wi-Fi. Disable Bluetooth. You want to sever the computer from your network so the infection cannot spread to your main servers or other workstations.
Step 2: Isolate Your Backups
Ransomware moves laterally. Once it infects one machine, it goes hunting for network drives, shared folders, and your backup servers. Hackers know that if they destroy your backups, you are much more likely to pay their ransom.
Take your backup systems offline immediately. If your backups are connected to the main network, the ransomware will try to encrypt them too. A clean, isolated backup is your absolute best defense right now. Protect it at all costs.
The Next Crucial Hours of Your Ransomware Response
Once you stop the bleeding, you have to start the triage process. This is where a lot of companies make critical mistakes by trying to handle everything internally instead of utilizing Scalable IT Services for Small Businesses.
Step 3: Call Your Cyber Insurance Provider
Unless you have a dedicated cybersecurity incident response firm on retainer, you need to bring in outside help. Your standard IT guy is probably not equipped to handle a targeted ransomware negotiation or the complex requirements of professional Malware Ransomware and Virus Removal Services in Delaware.
Reach out to your cyber insurance provider before you do anything else. They usually have a strict protocol and a list of approved vendors you must use to keep your coverage valid. If you try to fix the network yourself, you might accidentally void your policy.
Step 4: Document the Damage
Grab your smartphone and take photos of the ransom notes on the computer screens. Write down exactly which machines were infected and the exact time you noticed the issue.
Keep a detailed log of every action you and your team take. This documentation is crucial for law enforcement investigations and your insurance claim.
The Elephant in the Room: Should You Pay the Ransom?
This is the hardest question to answer during a crisis. Law enforcement agencies strictly advise against paying. Paying funds criminal organizations and paints a massive target on your back for future attacks.
Here is the reality. Sometimes businesses feel they have absolutely no choice. If your backups are destroyed and your hospital cannot access patient records, the calculus changes.
But you should never pay immediately. Threat actors often bluff about deleting data or releasing sensitive information. A professional ransomware negotiator can sometimes lower the price, buy you valuable time, or figure out if the hackers actually have a working decryption key. Yes, ransomware negotiators are a real profession. Rely on them.
Recovery and Post-Incident Action
Once the active threat is neutralized and the security vulnerability is closed, it is time to rebuild your network.
Step 5: Wipe and Restore from Clean Backups
Never try to simply clean the malware off the infected machines. You can never truly trust an operating system once it has been compromised by a threat actor.
You need to completely wipe the hard drives and reinstall the operating systems from scratch. Only then should you restore your data from a verified, clean backup. Make sure your IT team scans the backup data for dormant malware before bringing it back onto the live network.
Step 6: Find the Root Cause
How did they get in?
Was it a phishing email that an employee clicked? Did someone leave a remote desktop port open to the public internet? Did an employee reuse a compromised password?
If you do not find and fix the initial point of entry, the hackers will just walk right back through the exact same open door next week. Check out our guide on [how to secure remote access points] for more details on locking down your network perimeter.
How to Prevent the Next Incident
Surviving a cyber attack is exhausting. You never want to do it twice.
Now is the time to upgrade your defenses. Move away from basic antivirus software and invest in modern Endpoint Detection and Response tools. Implement strict multi-factor authentication for every single account in your company. No exceptions.
Most importantly, train your staff. Humans are always the weakest link in cybersecurity. Teach them how to spot suspicious emails, verify unusual requests, and report strange computer behavior immediately.
A ransomware attack is a brutal stress test for any organization. But if you follow a structured response plan, keep your head clear, and rely on the right experts, you can survive the crisis and come out stronger on the other side.